R. Paul Wilson On: Credit Card Scams (2/4)

Summarize this post
Editor’s Note: Although the UK is cracking down on credit card use in gambling, our UK-based readers will still benefit from reading the series as the scams can occur in any situation where you might use a credit or debit card.
This is the second of four articles detailing how credit, debit and bank cards might be compromised.

Players of online or live casinos depend on banking apps, online payments and credit cards so we need to remain informed and aware, whether they travel physically or digitally.
A common “feature” of modern debit and credit cards is their ease and speed of use. This makes using their cards increasingly simple – but that convenience might come at a cost to your security.
How Crooks Steal Your Money From Contactless Cards
“Touch to pay” systems – also known as “contactless” or “tap and pay” – depend on an RFID chip (that’s Radio Frequency Identification) inside many modern cards that can instantly transfer payment details to a terminal, without the need for a PIN number.
These transactions are often limited to around 30 pounds or dollars, but it offers criminals the opportunity to become “digital pickpockets”.
Simply by bringing a reader close to a wallet containing one or more cards, a thief might be able to charge any readable card without the owner ever knowing they’d been robbed.

When these cards were brand new, a hacker took me for a walk around London with a device in his briefcase that would detect any relevant RFID as he passed people on the street. When people walked by, the case was held close enough to scan pockets and suitably chipped bank cards were easily detected.
With a merchant account and a standard Chip and PIN device with an RFID detector, that device could theoretically be deconstructed and placed in an appropriate location where purses and pockets pass-by on a regular basis.
Imagine several of these built into the turnstiles of a stadium venue…
Over a year, millions of people will squeeze through those stiles and if the sensor was well-placed, any exposed cards could be charged by a random price generator.
If the crooks set up a non-existent coffee shop so they only charged each card a few dollars, victims might never notice (unless they never used that card).
Within a year, the bank who provided the merchant’s account may grow suspicious when a new coffee shop starts turning over millions of dollars (and other precautions are now in effect) but the principle is valid: if a “digital pickpocket” can scan enough cards for a low amount, he or she might never get caught and get away with a substantial amount.
The likelihood of this is very low, but I’ve seen several simple ways that touch payments have been compromised or abused.
A few of these are too sensitive to publish at this time but I heard of a remarkably simple scam when touch readers first appeared in the UK.
Real Life Example: Café Con
In a café in London, the shifty owner would tell people their first “tap” hadn’t worked and asked them to use their PIN or to sign a receipt as normal.
In fact, the first tap had worked so after the “second try” he had increased the bill by whatever he charged that first time. This was early in the lifespan of this system and the crooked café owner was caught, not by a suspicious customer but by the bank providing this service.
Payment systems are always vulnerable to abuse and if there’s a weakness in that system, providers are eager to detect them quickly. But a successful method for bypassing any form of security can sometimes exist for years before it spreads too far or becomes exposed through overuse.
This is why smart companies offer a bounty for experts who detect vulnerabilities and while such a policy might be fraught with its own problems, it can be an invaluable early warning system.
It’s Easy to Be Tricked
Some years ago, I gave a talk at Cambridge University and met with Professor Ross Anderson, whose team had publicly demonstrated that Chip and PIN could be compromised and who had a remarkably clear perspective on card security and the impact of increased consumer convenience.
The real issue was around who’s to blame when a card becomes compromised.
When funds are lost or stolen, banks would prefer to blame the end-user since they might have been careless about where and how they used their card.
But no system is completely secure and, as we will discuss in other articles, the weakest point in most forms of security is the human element.
It’s difficult to remain vigilant and mistakes are easy to make when using something like a bank card on a daily basis. Even the most suspicious of users (like me) could be taken by the right scam under the right circumstances.
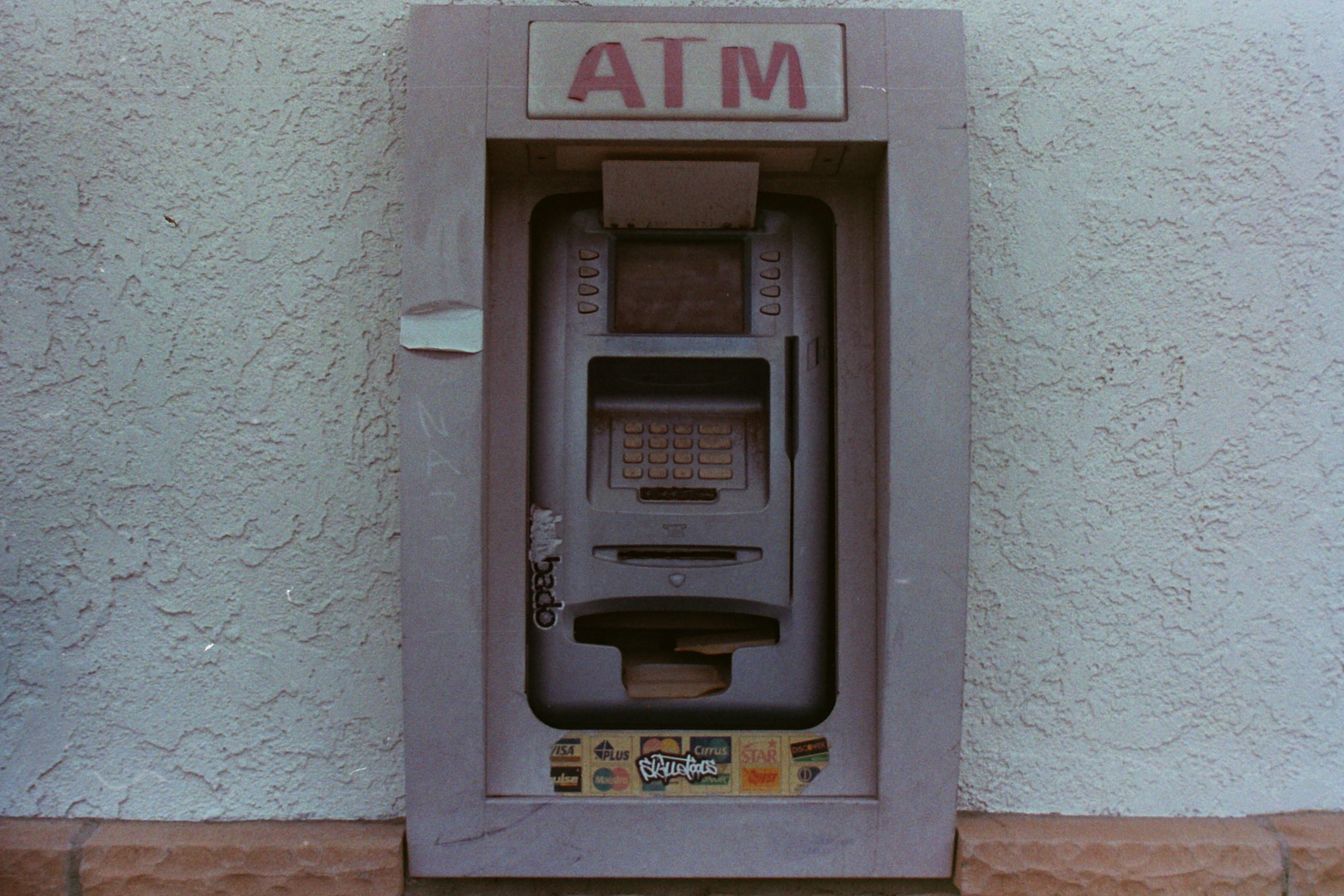
Consider that painted wooden ATM booth that we erected in London for The Real Hustle.

The result of using our fake device was that the machine simply failed to work and claimed to be out of order when it returned the victim’s card.
Everyone who used that machine simply went to the next available ATM and tried again, without any idea they had just given away their PIN number and allowed their card to be cloned.
Banks have been quick to blame customers when a fraudulent transaction depends on both card information and the supposedly secret PIN. Some would then refuse to return stolen funds, claiming the customer must have written down their number or given it to someone they shouldn’t.
In fact, there are many ways to steal both a card and a PIN number, which we illustrated on several Real Hustle items.
In many cases, the victim would have no idea that their PIN was recorded, captured, spotted or stolen either by someone with a telescope, a perfectly 3D-printed ATM, a keypad shell, a concealed camera or Uri Geller hidden in a van!
I am of the opinion that if your bank offers a product, they are responsible for the security and protection of that product – not just the customer who receives it.
Unless the bank can prove someone has been especially careless or cavalier with their cards and secret numbers, that bank should cover any losses from credit or debit card fraud.
Digital Deceptions
In my next article, I’ll discuss how bank and credit card details can be stolen over the phone or, thanks to the internet, via email.
Even if you’re a pretty clued up reader, don’t think for a second you might not get caught out or that there isn’t a scam (literally) with your name on it.


