New DDoS Threat ‘WireX’ Harnesses Android Devices, But Tech Companies Are Fighting Back
Posted on: September 3, 2017, 02:00h.
Last updated on: September 4, 2017, 09:17h.
Google was forced to remove around 300 Android apps from its Google Play Store this week after it emerged that they contained embedded malware that facilitated a new kind of distributed denial of service attack (DDoS), dubbed the WireX botnet.
Online gambling firms have been targets for DDoS attackers since the infancy of their industry, but the volume of attacks have increased in recent years and have also taken on more potent forms.
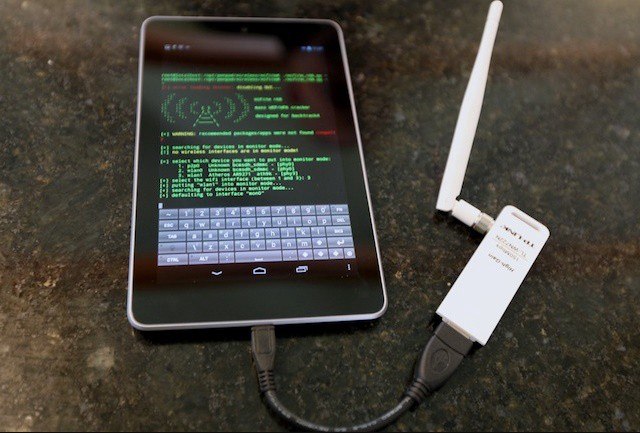
In simple terms, DDoS hackers are able to harness multiple compromised IP addresses, creating a “botnet,” which is then used to overwhelm a company’s website with thousands of meaningless requests for information. The attacks are malicious and intended to temporarily paralyze the website, often until a ransom is paid.
Sports betting and poker sites are prime targets because attackers can easily gauge peak business hours, such as during a major sporting event or a flagship poker tournament series.
70,000 Android Devices Compromised
Attacks are not just getting more powerful but more creative too, as in the case of WireX. The malware that permitted hackers to hijack an estimated 70,000 phones in 100 different countries was hidden in apparently innocuous apps offering ringtones, storage managers and media players.
WireX first came to the attention to cloud services provider Akamai on August 17, when a hospitality company was hit by an attack that was able to harness hundreds of thousands of IP addresses from around the world.
Since then, researchers from Akamai, Google, Cloudflare, Flashpoint, Oracle Dyn, RiskIQ and Team Cymru have been working together to take down the botnet. The collaboration is significant: a group of normally fragmented tech firms cooperating to beat the hackers.
Collaborative Effort
“These discoveries were only possible due to open collaboration between DDoS targets, DDoS mitigation companies, and intelligence firms,” Akamai said in a blog post. “Every player had a different piece of the puzzle; without contributions from everyone, this botnet would have remained a mystery.
“Once the larger collaborative effort began, the investigation began to unfold rapidly starting with the investigation of historic log information, which revealed a connection between the attacking IPs and something malicious, possibly running on top of the Android operating system,” it added.
In 2015, Akamai reported that the online gambling sector had overtaken the software and technology sector as that most frequently targeted by DDoS attackers, accounting for around 50 percent of attacks. The general increase has been driven by the availability of DDoS-for-hire sites, as well as hackers’ increasing willingness to post coding enabling attacks publicly on hacker forums.
Late year, the “Mirai” botnet, which harnessed devices connected to the Internet of Things, produced by far the most powerful DDoS attacks ever recorded. Its coding was uploaded onto the Hackforums website last October.
No comments yet