Global Cyber Ransomware Attacks Highlight Vulnerabilities of Unlicensed Gaming Operators
Posted on: May 15, 2017, 12:00h.
Last updated on: May 15, 2017, 11:52h.
A massive cyber ransomware attack is crippling computer networks operating on versions of Microsoft Windows. And while hackers are demanding money to unlock encrypted files, the total global take, for all the havoc that’s been wreaked, is surprisingly low: not even into the six-figure domain.
Hundreds of thousands of computers in more than 150 countries have been infected by the worm, which locks files and demands payment in order to restore the system. Though the US government says more than 4,000 ransomware aggressions occur each day, the scope of WannaCry, as this week’s cyber hit is being called, highlights the potential impact a successful criminal operation could have on an online gaming company.
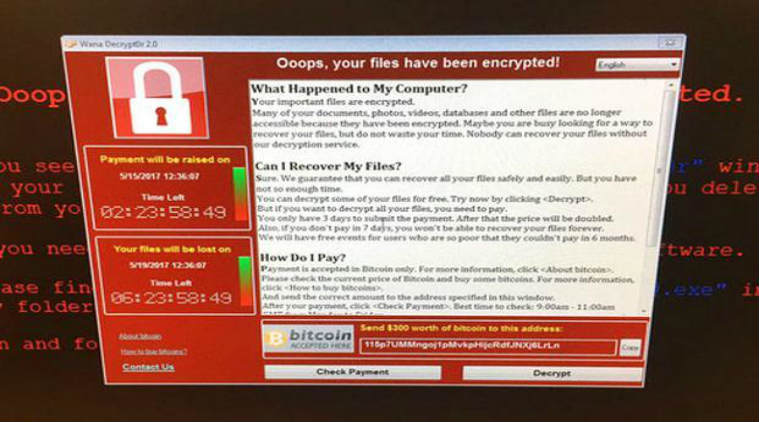
WannaCry spreads through outdated Microsoft systems, such as Windows XP and Windows Server 2003 or older. Once the malware reaches a vulnerable machine, it downloads an encryption package that locks up the computer’s files. When the user turns on the computer, a popup displays a demand for payment in Bitcoin, typically in the rage of $300 to $600. If the person doesn’t oblige, the price goes up. If payment never comes, the files are erased.
While the attack has been seen around the world, the hardest hit areas are reportedly in China, Germany, and the UK, the latter being home to many of the world’s largest online gaming companies. Should ransomware make its way into the network of one of the many gambling firms in Britain, say a William Hill or 888poker, digital accounts could potentially be impacted.
Don’t think it could happen? WannaCry’s infestation caused automaker Nissan to suspend manufacturing in Japan this week, and hospitals in Britain couldn’t accept patients, due to their computers going offline.
“Gambling sites that have a financial component are a particularly attractive target,” Kirk Soluk, a security expert, told the International Business Times this week.
WannaCry began when an unsuspecting user received an email containing a zip file. After the person downloaded the corrupt attachment, WannaCry’s campaign initiated.
Gambling Sites Targeted
As of Monday afternoon, there are no reports that internet gaming companies have been infected by WannaCry. However, it wouldn’t be unusual for cyber hackers to try to infiltrate one of the many networks linked to online casino operators.
It was reported just last week that numerous unlicensed online gambling websites in China were the victim of a distributed denial of service (DDoS) attack. Such cyber onslaughts essentially flood a website with requests until it shuts down. DDoS schemes have been one of the most common hacking techniques due to their relative simplicity. In fact, those on the Deep Web can hire a hacker for less than a $100 to perform an illegal cyber invasion.
William Hill was targeted last fall and its gambling services were knocked offline for nearly a day. In 2015, four New Jersey online gaming sites were disrupted by DDoS plots, as was PokerStars, Betfair, Unibet, and Svenska Spel. In all of these cases, hackers demanded ransom to cease the rush of data, but security experts were able to combat the attack without paying.
Don’t Pay, Say Experts
Security experts and government officials say not to pay ransom when a computer becomes infected. Of course, that’s easier said than done for those who haven’t backed up their files on an external drive. A White House spokesman said on Monday during a press briefing that criminals behind WannaCry had received less than $70,000 in ransom.
That number might increase, of course, as more computers become infected.
When one computer is compromised, it immediately spreads to every other machine on that network. Ransomware exploits a Windows security flaw that has since been addressed in a “patch,” but those who haven’t updated their systems, or who use unlicensed software, remain at risk.
No comments yet